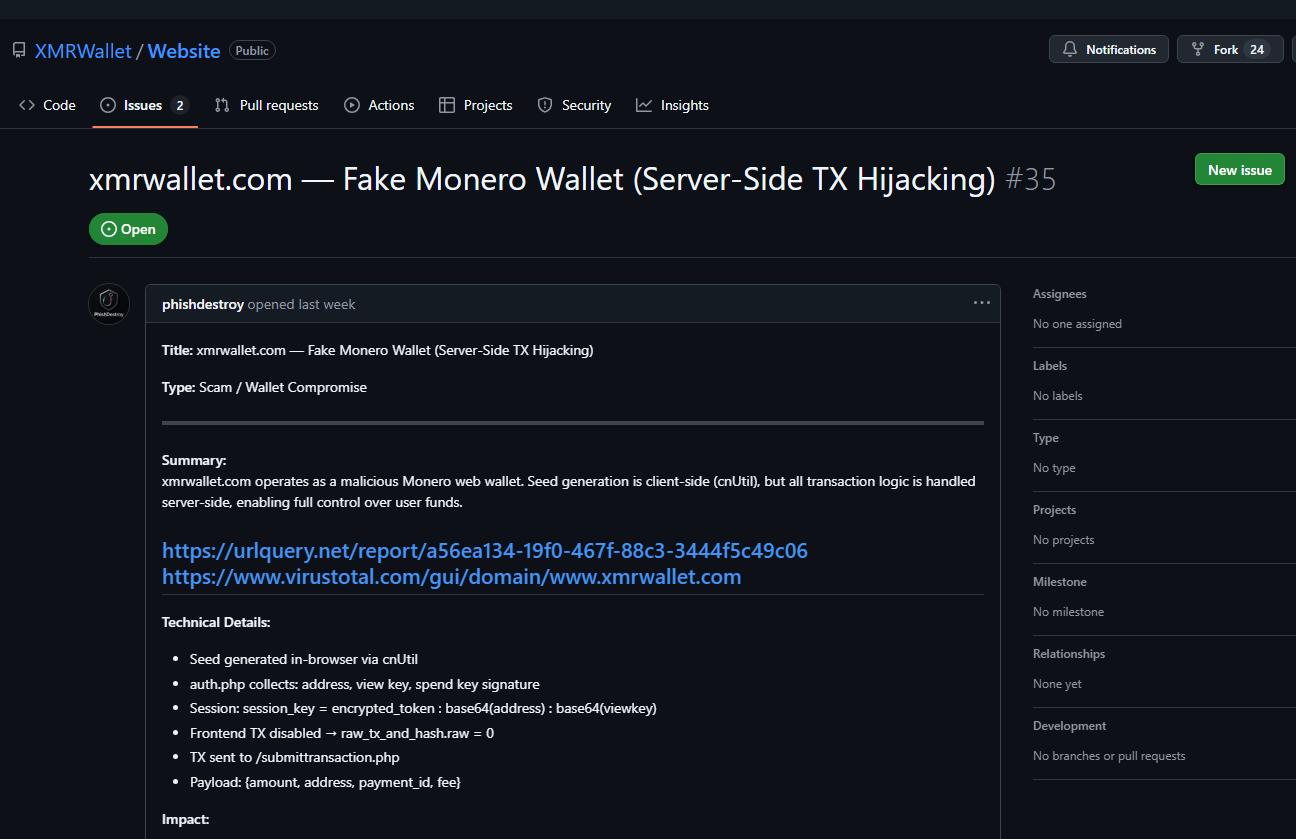
ISSUE #35
ORIGINAL SCREENSHOTS
Captured before deletion. Status: Open at time of capture. Deleted by operator after both domains were suspended.
Summary
xmrwallet.com operates as a malicious Monero web wallet. Seed generation is client-side (cnUtil), but all transaction logic is handled server-side, enabling full control over user funds.
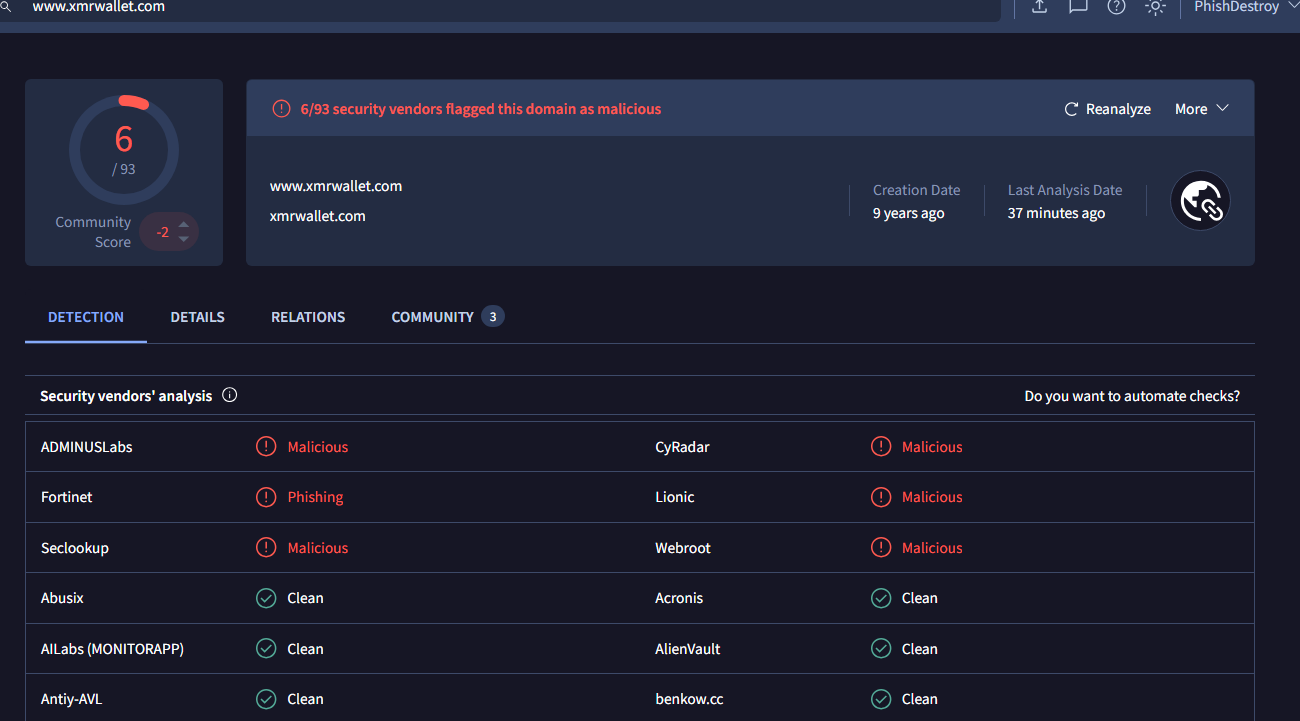
External scans: urlquery.net → virustotal.com →
Technical Details
- Seed generated in-browser via
cnUtil auth.phpcollects: address, view key, spend key signature (verification)- Session:
session_key = encrypted_token : base64(address) : base64(viewkey) - Frontend TX disabled → raw_tx_and_hash.raw = 0
- TX sent to
/submittransaction.phpwith metadata only - Payload:
{amount, address, payment_id, fee}— server builds actual TX
Impact
- Server builds + broadcasts TX using server-held keys
- Destination address can be silently modified to any address
- Full fund compromise — victim UI shows no valid TxID for stolen funds
Infrastructure
- IP: 186.2.165.49 (DDoS-Guard, AS59692) · NS: ns1/ns2.ddos-guard.net
- Backend: Apache/2.4.58 (Ubuntu) · PHP 8.2.29
- Registrar: NameSilo (2016 → 2031) · SSL: Let's Encrypt (Jan 2026)
- Hosting: IQWeb FZ-LLC (offshore, abuse-resistant) · $550+/month custom plan
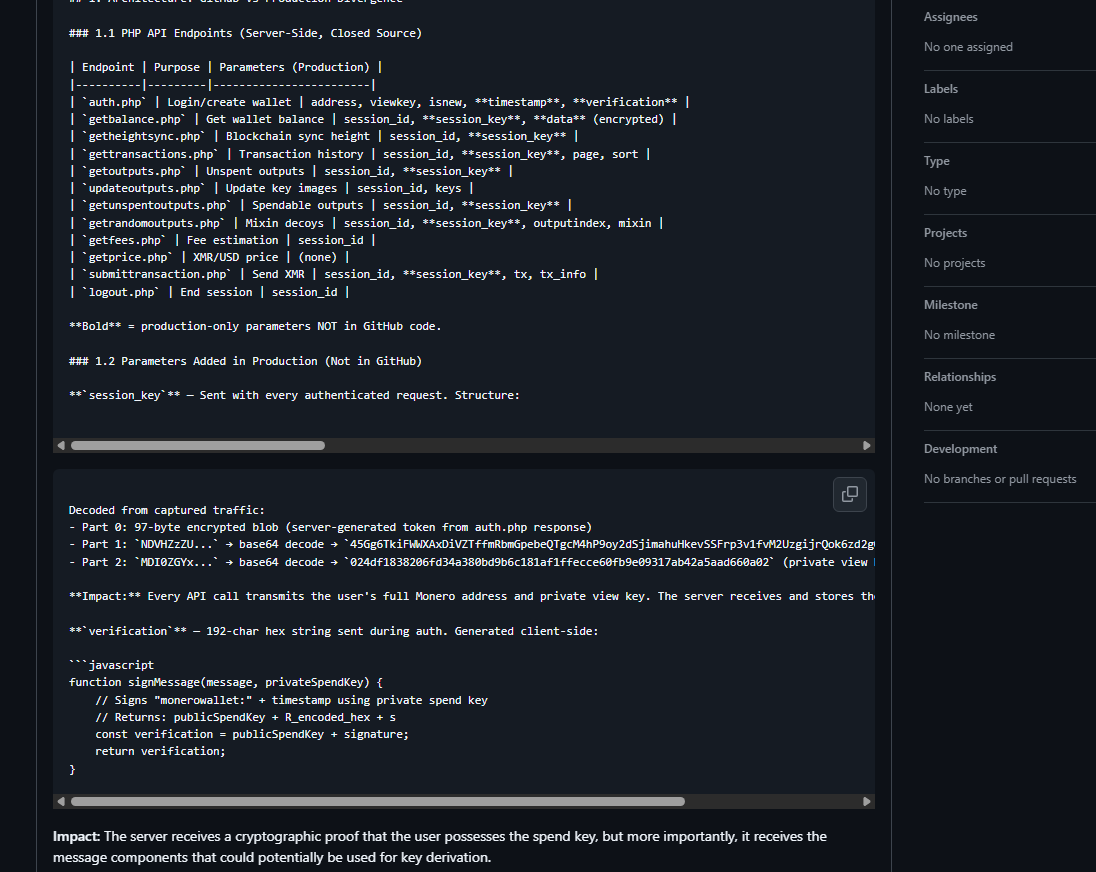
§1.1 PHP API Endpoints — GitHub vs Production
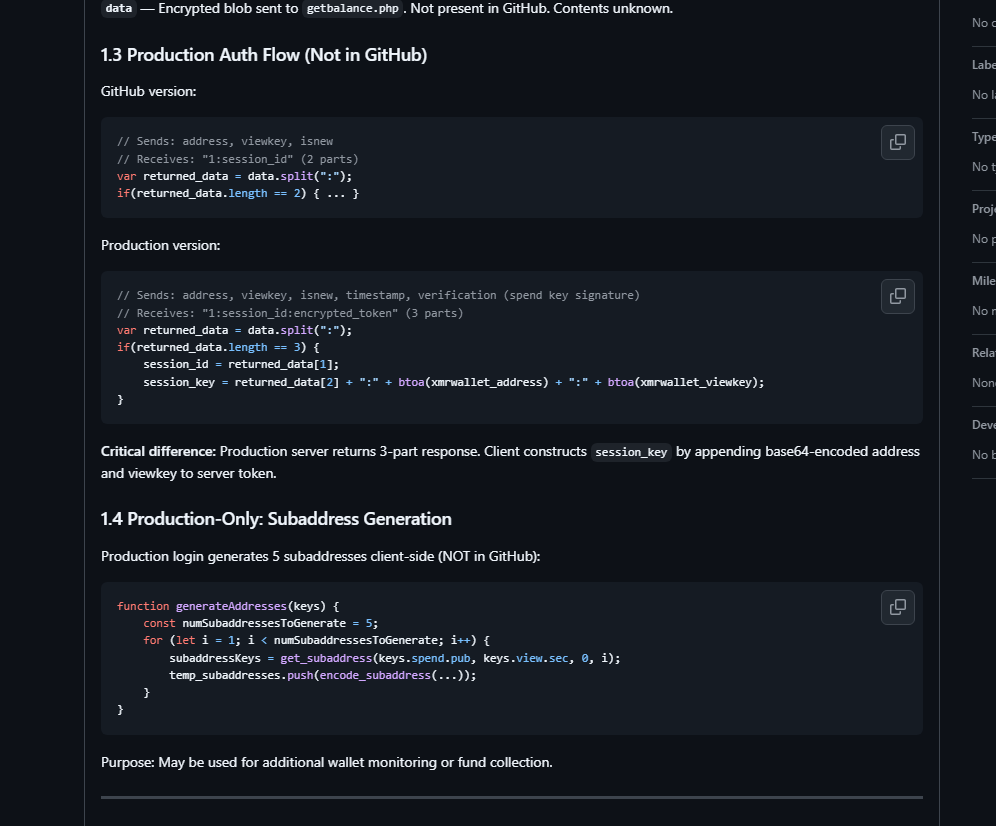
§1.2 session_key Decoded
§1.3 Production Auth Flow (NOT in GitHub)
§2 The Fraud Mechanism — TX Signing Bypass (raw_tx_and_hash.raw = 0)
The "swept" Transaction Type — Theft Marker
§3 Code Evolution — 5.3 Year Secret Development Gap
§4 Loss Estimation
- Documented losses (named victims): 674+ XMR (~$227K+ USD)
- Single incident (Sitejabber): 590 XMR stolen
- Conservative total estimate: 5,000–50,000+ XMR ($1.5M–$15M+ at historical prices)
- 10,000–50,000+ wallet accounts created over 8 years of operation
§5 Cover-Up Evidence
- 5.3 year public commit gap while production evolves
- 21+ GitHub issues deleted by operator (confirmed)
- "Sync problems" cover story directed at every theft victim
- Blog post: "5 Crypto Scams You Should Know About" — legitimacy shield
- Claims "free, funded solely by donations" — zero donation wallet exists
- 50+ paid SEO articles purchasing top Google rankings
- $550+/month IQWeb custom hosting — funded by stolen XMR
IOCs
- xmrwallet.com (NameSilo, active) · xmrwallet.cc (✘ suspended) · xmrwallet.biz (✘ suspended)
- IP: 186.2.165.49 · CDN: DDoS-Guard AS59692
- GA: UA-116766241-1 · GTM · DoubleClick · GA4
- MX: mx1/mx2.privateemail.com (identical on all 3 domains — single operator proof)
- Google Verify: d-En_D3kMw6CqZpPwZeDn4ICI5Tyk1WvPYdVdGzEWr8
Operator
- Nathalie Roy · Canada
- GitHub: nathroy (ID: 39167759, created 2018-05-10)
- Reddit: u/WiseSolution — banned from r/Monero
- Emails: admin@, support@, feedback@, lr@xmrwallet.com, royn5094@protonmail.com
- Self-identified on support.html: "Nathalie Roy created XMRWallet..."
Prepared by PhishDestroy · 2026-02-15 · OSINT only · no unauthorized access · github.com/phishdestroy/destroylist